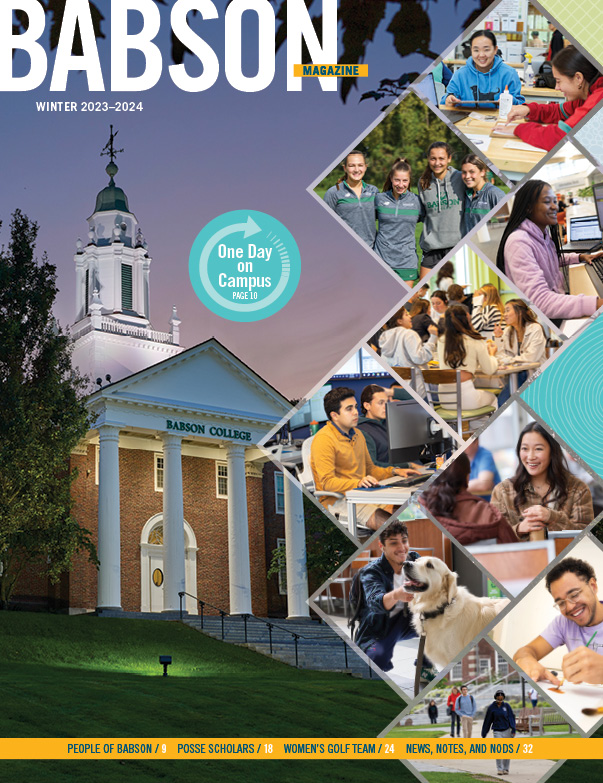
All in One Day: What Happens on Campus
From sunrise to way past sunset, Babson’s Wellesley campus buzzes with activity—from the classrooms to the Commons, from the dining hall to the creative spaces, from the community meetings to the athletic fields. Here’s what happens during one typical September day.

The Enduring Impact of Babson’s Posse Scholars
For 20 years, Babson College’s partnership with the Posse Foundation has provided opportunity and opened doors for students in New York City with leadership potential. Here, we catch up with four exemplary Posse alumni to illustrate the immeasurable impact on the scholars, the College, and their communities.

From the President: Perpetually Aspirational
Babson College has ascended to a new leadership position across higher education after being ranked the 10th best college in the country by The Wall Street Journal. This unprecedented accolade affirms that entrepreneurship has evolved from a competency that can be taught to one that must be taught.